1. A network engineer is implementing a network design using VLSM for network 192.168.1.0/24. After subnetting the network, the engineer has decided to take one of the subnets, 192.168.1.16/28 and subnet it further to provide for point-to-point serial link addresses. What is the maximum number of subnets that can be created from the 192.168.1.16/28 subnet for serial connections?
• 1
• 2
• 4
• 6
• 8
• 16
2. When running NAT, what is the purpose of address overloading?
• limit the number of hosts that can connect to the WAN
• allow multiple inside addresses to share a single global address
• force hosts to wait for an available address
• allow an outside host to share inside global addresses
3. What two advantages does CIDR provide to a network? (Choose two.)
• reduced routing table size
• dynamic address assignment
• automatic route redistribution
• reduced routing update traffic
• automatic summarization at classful boundaries
4. How does a router keep track of which inside local address is used when NAT overload is configured?
• The router adds an additional bit to the source IP address and maintains a separate table.
• The router modifies the QoS field.
• The router uses TCP or UDP port numbers.
• The router uses a manual entry that is created and maintained in the database of the router.
5. What is a characteristic of a classful routing protocol on the network?
• All subnets are seen by all routers.
• CIDR addresses are advertised.
• A subnet can be further subnetted down and advertised correctly.
• Updates received by a router in a different major network have the default mask applied.
6. Refer to the exhibit. Which address is an inside global address?
• 10.1.1.1
• 10.1.1.2
• 198.18.1.55
• 64.100.0.1
7. Refer to the exhibit. All networks that are shown have a /24 prefix. Assuming that all routes have been discovered by all routers in the network, which address will successfully summarize only the networks that are shown?
• 192.168.8.0/21
• 192.168.8.0/24
• 192.168.16.0/20
• 192.168.16.0/21
• 192.168.16.0/24
8. What is the CIDR prefix designation that summarizes the entire reserved Class B RFC 1918 internal address range?
• /4
• /8
• /12
• /16
• /20
9. Which NAT term refers to the IP address of your inside host as it appears to the outside network?
• inside global IP address
• outside global IP address
• inside local IP address
• outside local IP address
172.16.1.0/21 manufacturing
172.16.1.0/22 sales
172.16.3.0/26 research
• 172.16.48.0/19 head office
172.16.16.0/20 manufacturing
172.16.48.128 sales
172.16.48.0/26 research
• 172.16.2.0/23 head office
172.16.4.0/23 manufacturing
172.16.6.0/24 sales
172.16.7.0/26 research
• 172.16.2.0/22 head office
172.16.3.0/23 manufacturing
172.16.4.0/26 sales
172.16.4.128/25 research
11. A company using a Class B IP addressing scheme needs as many as 100 subnetworks. Assuming that variable length subnetting is not used and all subnets require at least 300 hosts, what subnet mask is appropriate to use?
• 255.255.0.0
• 255.255.240.0
• 255.255.254.0
• 255.255.255.0
• 255.255.255.128
• 255.255.255.192
12. Host A in the exhibit is assigned the IP address 10.118.197.55/20. How many more network devices can be added to this same subnetwork?
• 253
• 509
• 1021
• 2045
• 4093
13. Refer to the exhibit. RIP version 2 is configured as the network routing protocol and all of the default parameters remain the same. Which update is sent from R2 to R3 about the 10.16.1.0/24 network connected to R1?
• 10.16.0.0/16
• 10.0.0.0/24
• 10.0.0.0/8
• 10.16.1.0/24
14. What range of networks are summarized by the address and mask, 192.168.32.0/19?
• 192.168.0.0/24 - 192.168.32.0/24
• 192.168.0.0/24 - 192.168.31.0/24
• 192.168.32.0/24 – 192.168.64.0/24
• 192.168.32.0/24 – 192.168.63.0/24
15. Refer to the exhibit. Based on the output of the show ip nat translations command, which kind of address translation is in effect on this router?
• static
• public
• overload
• private
16. How many addresses will be available for dynamic NAT translation when a router is configured with the following commands?
• Router(config)#ip nat pool TAME 209.165.201.23 209.165.201.30 netmask 255.255.255.224
• Router(config)#ip nat inside source list 9 pool TAME
• 7
• 8
• 9
• 10
• 24
• 31
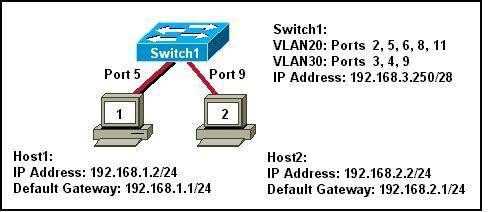
17. Refer to the exhibit. Which two IP addresses could be assigned to the hosts that are shown in the exhibit? (Choose two.)
• 192.168.65.31
• 192.168.65.32
• 192.168.65.35
• 192.168.65.60
• 192.168.65.63
• 192.168.65.64
18. What are the network and broadcast addresses for host 192.168.100.130/27? (Choose two.)
• network 192.168.100.0
• network 192.168.100.128
• network 192.168.100.130
• broadcast 192.168.100.157
• broadcast 192.168.100.159
• broadcast 192.168.100.255
19. Refer to the exhibit. Which two are valid VLSM network addresses for the serial link between Router1 and Router2? (Choose two.)
• 192.168.1.4/30
• 192.168.1.8/30
• 192.168.1.90/30
• 192.168.1.101/30
• 192.168.1.190/30
20. When configuring NAT on a Cisco router, what is the inside local IP address?
• the IP address of an inside host as it appears to the outside network
• the IP address of an outside host as it appears to the inside network
• the IP address of an inside host as it appears to the inside network
• the configured IP address assigned to a host in the outside network